This section allows you to view all posts made by this member. Note that you can only see posts made in areas you currently have access to.
46
Waroeng English / Please translate to Indonesian
« on: 26 August 2009, 11:26:38 AM »lagi di kantor gak boleh denger gede gede suaranya
 bisa bantu terjemahin..
bisa bantu terjemahin.. 
47
Seremonial / chubby ulang tahun yg ke 20
« on: 25 August 2009, 08:39:11 PM »
besok 26 Agustus chubby 王思茄 ultah euyyyyyyy





















met ultah ya....




















met ultah ya....
48
Ulasan Buku, Majalah, Musik atau Film / Ebook - Questions of Sakka
« on: 22 August 2009, 01:56:16 PM »
The Questions of Sakka
A Discourse by
Venerable Mahæsø Sayædaw
An Abridged Translation by
U Aye Maung
Printed for free Distribution by
ASSOCIATION FOR INSIGHT MEDITATION
3 Clifton Way • Alperton • Middlesex • HA0 4PQ
Website: AIMWELL.ORG Email: pesala [at] aimwell.org
Buddha Sæsanænuggaha Organisation
Mahæsø Translation Committee, Rangoon
The Questions of Sakka
A Discourse on Sakkapañha Sutta
by
Venerable Mahæsø Sayædaw
An Abridged Translation
by U Aye Maung
First printed and published in the Socialist
Republic of the Union of Burma
December 1980
Pocket Edition
Edited by Bhikkhu Pesala
Reprinted June 2002
Cover Illustration by Christine Fitzmaurice
The illustrations are copyright.
About the Association for Insight Meditation
The Association was set up in September
1995 to promote the practice of vipassanæ
meditation in the Mahæsø tradition. The
Association also aims to publish selected
books and booklets on satipa¥¥hæna
vipassanæ meditation to promote understanding
of the practice of mindfulness.
“The Questions of Sakka” was first
published by the Association in 1996.
The Spiritual Director of the Association,
Bhikkhu Pesala, was ordained by
the Venerable Mahæsø Sayædaw in 1979,
and has been to Burma four times for
intensive meditation practice.
If you would like information about
other publications or insight meditation classes and retreats in the
Burmese tradition, please see our website:
http://www.aimwell.org
email: pesala [at] aimwell.org
A Discourse by
Venerable Mahæsø Sayædaw
An Abridged Translation by
U Aye Maung
Printed for free Distribution by
ASSOCIATION FOR INSIGHT MEDITATION
3 Clifton Way • Alperton • Middlesex • HA0 4PQ
Website: AIMWELL.ORG Email: pesala [at] aimwell.org
Buddha Sæsanænuggaha Organisation
Mahæsø Translation Committee, Rangoon
The Questions of Sakka
A Discourse on Sakkapañha Sutta
by
Venerable Mahæsø Sayædaw
An Abridged Translation
by U Aye Maung
First printed and published in the Socialist
Republic of the Union of Burma
December 1980
Pocket Edition
Edited by Bhikkhu Pesala
Reprinted June 2002
Cover Illustration by Christine Fitzmaurice
The illustrations are copyright.
About the Association for Insight Meditation
The Association was set up in September
1995 to promote the practice of vipassanæ
meditation in the Mahæsø tradition. The
Association also aims to publish selected
books and booklets on satipa¥¥hæna
vipassanæ meditation to promote understanding
of the practice of mindfulness.
“The Questions of Sakka” was first
published by the Association in 1996.
The Spiritual Director of the Association,
Bhikkhu Pesala, was ordained by
the Venerable Mahæsø Sayædaw in 1979,
and has been to Burma four times for
intensive meditation practice.
If you would like information about
other publications or insight meditation classes and retreats in the
Burmese tradition, please see our website:
http://www.aimwell.org
email: pesala [at] aimwell.org
49
Kafe Jongkok / RPG Video - Choose a different Ending
« on: 21 August 2009, 04:14:15 PM »
hehe.............. ada ada ajee...... 

50
hehe.. iseng iseng maenan lama....
http://sodaplay.com/
disitu kita bisa bikin rancang bangun... lumayan buat iseng2
http://sodaplay.com/
disitu kita bisa bikin rancang bangun... lumayan buat iseng2
51
Sains / New exoplanet orbits 'backwards' ......... :O :O :O
« on: 15 August 2009, 10:19:43 AM »
source : http://news.bbc.co.uk/2/hi/science/nature/8197683.stm
By Paul Rincon
Science reporter, BBC News

Planets with retrograde orbits should be rare
Astronomers have discovered the first planet that orbits in the opposite direction to the spin of its star.
Planets form out of the same swirling gas cloud that creates a star, so they are expected to orbit in the same direction that the star rotates.
The new planet is thought to have been flung into its "retrograde" orbit by a close encounter with either another planet or with a passing star.
The work has been submitted to the Astrophysical Journal for publication.
Co-author Coel Hellier, from Keele University in Staffordshire, UK, said planets with retrograde orbits were thought to be rare.
"With everything [in the star system] swirling around the same way and the star spinning the same way, you have to do quite a lot to it to make it go in the opposite direction," he told BBC News.
The direction of orbit is known for roughly a dozen exoplanets (planets outside our solar system). This is the only example with a retrograde orbit. All others are prograde; they orbit in the same direction as the spin of their star.
Close encounters
Professor Hellier said a near-collision was probably responsible for this planet's unusual orbit.
"If you have a near-collision, then you'll have a large gravitational slingshot from that interaction," he explained.
"This is the likeliest explanation. But it might be possible you can do it by gradually perturbing the orbit through the influence of a second planet. So far, we haven't found any evidence of a second planet there."
The new object has been named WASP-17b. It is the 17th exoplanet to have been discovered by the Wide Area Search for Planets (WASP) consortium of UK universities.
The gas giant is about twice the size of Jupiter, but has about half the mass. This bloatedness might also be rooted in the close encounter that changed the planet's direction.
WASP-17b was detected using an array of cameras set up to monitor hundreds of thousands of stars.
Astronomers were searching for small dips in light from these stars that occur when a planet passes in front of them. When this happens, the planets are said to transit their parent star.
A team from Geneva Observatory in Switzerland then looked for spectral signs that the star was wobbling due to gravitational tugs from an orbiting planet.
"If you look at how the spectrum of the star changes when the planet transits across it, you can work out which way the planet is travelling," Professor Hellier added.
"That allows you to prove that it's in a retrograde orbit."
The size of the dip in light from the star during the transit allowed astronomers to work out the planet's radius.
To work out how massive it was, they recorded the motion of the star as it was tugged on by the orbiting planet.
Paul.Rincon-INTERNET [at] bbc.co.uk
By Paul Rincon
Science reporter, BBC News

Planets with retrograde orbits should be rare
Astronomers have discovered the first planet that orbits in the opposite direction to the spin of its star.
Planets form out of the same swirling gas cloud that creates a star, so they are expected to orbit in the same direction that the star rotates.
The new planet is thought to have been flung into its "retrograde" orbit by a close encounter with either another planet or with a passing star.
The work has been submitted to the Astrophysical Journal for publication.
Co-author Coel Hellier, from Keele University in Staffordshire, UK, said planets with retrograde orbits were thought to be rare.
"With everything [in the star system] swirling around the same way and the star spinning the same way, you have to do quite a lot to it to make it go in the opposite direction," he told BBC News.
The direction of orbit is known for roughly a dozen exoplanets (planets outside our solar system). This is the only example with a retrograde orbit. All others are prograde; they orbit in the same direction as the spin of their star.
Close encounters
Professor Hellier said a near-collision was probably responsible for this planet's unusual orbit.
"If you have a near-collision, then you'll have a large gravitational slingshot from that interaction," he explained.
"This is the likeliest explanation. But it might be possible you can do it by gradually perturbing the orbit through the influence of a second planet. So far, we haven't found any evidence of a second planet there."
The new object has been named WASP-17b. It is the 17th exoplanet to have been discovered by the Wide Area Search for Planets (WASP) consortium of UK universities.
The gas giant is about twice the size of Jupiter, but has about half the mass. This bloatedness might also be rooted in the close encounter that changed the planet's direction.
WASP-17b was detected using an array of cameras set up to monitor hundreds of thousands of stars.
Astronomers were searching for small dips in light from these stars that occur when a planet passes in front of them. When this happens, the planets are said to transit their parent star.
A team from Geneva Observatory in Switzerland then looked for spectral signs that the star was wobbling due to gravitational tugs from an orbiting planet.
"If you look at how the spectrum of the star changes when the planet transits across it, you can work out which way the planet is travelling," Professor Hellier added.
"That allows you to prove that it's in a retrograde orbit."
The size of the dip in light from the star during the transit allowed astronomers to work out the planet's radius.
To work out how massive it was, they recorded the motion of the star as it was tugged on by the orbiting planet.
Paul.Rincon-INTERNET [at] bbc.co.uk
52
Politik, ekonomi, Sosial dan budaya Umum / China ditches compulsory Green Dam plans
« on: 15 August 2009, 10:11:18 AM »
source = http://www.itnews.com.au/News/152924,china-ditches-compulsory-green-dam-plans.aspx
By Rosalie Marshall
Aug 14, 2009 12:19 AM
Tags: green | dam | internet | software | china | filter | censorship | security
Internet filtering technology now voluntary.
China has ditched plans to force foreign and domestic computer manufacturers to install internet filtering technology in computers sold inside its borders.
The Chinese government paid US$5.85 million to develop the software called Green Dam and claimed it was being installed to stop access to porn on computers and protect children.
But some argued the initiative would also further China’s online censorship programme, already the most advanced in the world, making it controversial for western computer manufacturers and human rights organisations.
China’s industry and information technology minister Li Yizhong said manufacturers, internet users and organisations opposed to the plans had received the wrong message from his department and that installation was never planned to be compulsory.
He said Green Dam would be installed in public places and schools, but would be “voluntary” for other users who can choose whether to install a software disk that they will receive when buying a new computer.
"Any move to politicise the issue or to attack China's Internet management system is irresponsible and not in line with reality", he said in a statement on the Chinese government's English web portal.
All new computers in China were originally meant to have Green Dam installed by 1 July, but in June the mandate to comply with the government’s intentions was delayed because the government acknowledged PC manufacturers needed more time to conform.
However, other reports have said the delay was due to the fact that the Green Dam software faced opposition from internet users claiming their privacy and internet freedoms would be curbed by its installation.
Green Dam has also faced legal problems. US software filtering provider Solid Oak claimed copyright infringement, alleging programming code from its software CyberSitter was found in the Green Dam application.
Copyright © 2009 vnunet.com
By Rosalie Marshall
Aug 14, 2009 12:19 AM
Tags: green | dam | internet | software | china | filter | censorship | security
Internet filtering technology now voluntary.
China has ditched plans to force foreign and domestic computer manufacturers to install internet filtering technology in computers sold inside its borders.
The Chinese government paid US$5.85 million to develop the software called Green Dam and claimed it was being installed to stop access to porn on computers and protect children.
But some argued the initiative would also further China’s online censorship programme, already the most advanced in the world, making it controversial for western computer manufacturers and human rights organisations.
China’s industry and information technology minister Li Yizhong said manufacturers, internet users and organisations opposed to the plans had received the wrong message from his department and that installation was never planned to be compulsory.
He said Green Dam would be installed in public places and schools, but would be “voluntary” for other users who can choose whether to install a software disk that they will receive when buying a new computer.
"Any move to politicise the issue or to attack China's Internet management system is irresponsible and not in line with reality", he said in a statement on the Chinese government's English web portal.
All new computers in China were originally meant to have Green Dam installed by 1 July, but in June the mandate to comply with the government’s intentions was delayed because the government acknowledged PC manufacturers needed more time to conform.
However, other reports have said the delay was due to the fact that the Green Dam software faced opposition from internet users claiming their privacy and internet freedoms would be curbed by its installation.
Green Dam has also faced legal problems. US software filtering provider Solid Oak claimed copyright infringement, alleging programming code from its software CyberSitter was found in the Green Dam application.
Copyright © 2009 vnunet.com
53
Teknologi Informasi / The Biggest Security Hole on the Web?
« on: 15 August 2009, 09:55:36 AM »
source : http://www.webpronews.com/topnews/2009/08/13/the-biggest-security-hole-on-the-web
 Security Company Points to Flash/Acrobat Reader Vulnerabilities
Security Company Points to Flash/Acrobat Reader Vulnerabilities
Two weeks ago, Adobe released a critical patch for Flash Player and Acrobat Reader. According to online security company Trusteer, about 80% of users are still vulnerable, and perhaps more startling, the company views this as being possibly the biggest security hole on the Internet today.
That 80% figure is based on Trusteer's installed base of over 2.5 million online banking users of the company's security service.
"The penetration of Adobe Flash and Acrobat is unparalleled," a spokesperson for Trusteer tells WebProNews. "According to Adobe, 99% of Internet users run Flash.
So so many people on the web are running Flash, and Adobe released the patch two weeks ago, why are so many still vulnerable? Trusteer thinks Adobe just has issues with distributing patches.
"Adobe is facing some major security challenges and one of its biggest hurdles is its software update mechanism. For some reason, it is not effective enough in distributing security patches to the field," says Trusteer CEO Mickey Boodaei. "Given the lack of attention this situation has received to date, it appears that few people understand the magnitude of the problem. We recommend that all enterprises and individuals install the latest Flash and Acrobat updates immediately."
Accoreding to Trusteer, targeting products like Flash and Acrobat is attractive to wrongdoers because they reach such a huge portion of Internet users. Browser use is much more diversified with Internet Explorer reaching about 65% of users and Firefox reaching 30%. Targeting Adobe's products just covers a lot more people.
 Security Company Points to Flash/Acrobat Reader Vulnerabilities
Security Company Points to Flash/Acrobat Reader VulnerabilitiesTwo weeks ago, Adobe released a critical patch for Flash Player and Acrobat Reader. According to online security company Trusteer, about 80% of users are still vulnerable, and perhaps more startling, the company views this as being possibly the biggest security hole on the Internet today.
That 80% figure is based on Trusteer's installed base of over 2.5 million online banking users of the company's security service.
"The penetration of Adobe Flash and Acrobat is unparalleled," a spokesperson for Trusteer tells WebProNews. "According to Adobe, 99% of Internet users run Flash.
So so many people on the web are running Flash, and Adobe released the patch two weeks ago, why are so many still vulnerable? Trusteer thinks Adobe just has issues with distributing patches.
"Adobe is facing some major security challenges and one of its biggest hurdles is its software update mechanism. For some reason, it is not effective enough in distributing security patches to the field," says Trusteer CEO Mickey Boodaei. "Given the lack of attention this situation has received to date, it appears that few people understand the magnitude of the problem. We recommend that all enterprises and individuals install the latest Flash and Acrobat updates immediately."
Accoreding to Trusteer, targeting products like Flash and Acrobat is attractive to wrongdoers because they reach such a huge portion of Internet users. Browser use is much more diversified with Internet Explorer reaching about 65% of users and Firefox reaching 30%. Targeting Adobe's products just covers a lot more people.
54
Teknologi Informasi / Microsoft IE 8 shines in Web browser security test
« on: 15 August 2009, 09:51:40 AM »
source = http://www.networkworld.com/cgi-bin/mailto/x.cgi?pagetosend=/export/home/httpd/htdocs/news/2009/081309-microsoft-ie8-browser-security.html&pagename=/news/2009/081309-microsoft-ie8-browser-security.html&pageurl=http://www.networkworld.com/news/2009/08
Firefox a close second in test paid for by Microsoft
By Ellen Messmer , Network World , 08/13/2009
Microsoft's Internet Explorer 8 rated tops among five browsers tested by NSS Labs for effectiveness in protecting against malware and phishing attacks—though NSS Labs acknowledges Microsoft paid for the tests.
Nevertheless, the test process, which lasted over a two-week period in July at the NSS Labs in Austin, evaluated the browsers based on access to live Internet sites and in theory could be duplicated elsewhere. Apple Safari 4, Google Chrome 2, Mozilla Firefox 3, and Opera 10 beta were evaluated as being behind Microsoft IE 8 when it comes to browser protection against phishing and malware, mainly because Microsoft was deemed more speedy and comprehensive in delivering updates about known phishing and malware to the user's desktop browser.
Slideshow: 15 Secrets of Next-Gen Browsers
Time is of the essence to use the browser as protective cover, one of the two NSS Labs reports issued Thursday notes. The report cites an Anti-Phishing Working Group estimate that more than 47,000 unique attacks occurred in the second half of 2008 with an average lifespan of 52 hours.
The test was based on 593 validated URLs. "The average phishing URL catch rate for browsers over the entire 14-day test period ranged from 2% for Safari 4 to 83% for Windows Internet Explorer 8," the test report states. "Internet Explorer 8 and Firefox 3 were the most consistent in the high level of protection they offered."
Firefox 3, which boasted 80% effectiveness in the phishing test, finished just behind IE 8's 83%. Coming in at third was the Opera 10 beta at 54%, followed by Chrome 2 at 26% and Safari 4 at 2 % in terms of mean block rate for phishing.
"Google Chrome's overall catch rate of 26% was below average," the "Web Browser Security: Phishing Comparison Comparative Results" report concludes. "We expected better results given the fanfare about Google's SafeBrowsing initiative . Additionally, a third-party (Firefox) was able to utilize Google API to achieve significantly better protection than Google's own browser."
In the testing for how well each of the five browsers provide protection against socially-engineered malware—defined as a Web page link that leads directly to a ‘download' that delivers a malicious payload whose content type would lead to execution—Microsoft was also found to perform the best.
In a test based on 608 potentially malicious URLs, IE 8 achieved an 81% mean block rate for socially-engineered malware, while Firefox 3 logged in at 27%, Safari 4 at 21%, Chrome 2 at 7% and Opera 10 beta at 1%. On average, 197 new validated URLs were added to the test each day, more or less depending on "criminal activity levels" as malicious URLs quickly rolled in and out of use.
IE Explorer 8, which calls its protection mechanism SmartScreen , did best for protecting against socially-engineered malware in what was called the "zero hour" timeframe when a malicious URL was spotted by blocking 51% of the time. By the fifth day of the known malicious URL, IE 8 was blocking 91% of the time, Firefox 3 24%, Safari 4 22% , Chrome 2 14% and Opera 10 beta 1%.
The report titled "Web browser Security: Socially Engineered Malware Protection Comparative Results 2nd Edition," points out that browser protection relies on two main functional components:
"an in-the-cloud reputation-based system which scours the Internet for malicious websites and categorizes content according" by adding it to a black or white list, or assigning a ‘score,' depending on the vendor's approach, which might be automated or manual or a combination of both.
"The second functional component resides with the Web browser and requests reputation information from in-the-cloud systems about specific URLs and then enforces warning and blocking functions."
Rick Moy, president of NSS Labs, says IE is continuing to improve its protection against cybercriminals based on a comparison with previous tests. The four other browsers in the tests generally "underperformed," he notes, with the exception of the Firefox browser phishing scores.
Moy says the Web browser is often viewed in terms of its potential vulnerabilities but it should also be looked at as "a potential layer of security."
All contents copyright 1995-2009 Network World, Inc. http://www.networkworld.com
Firefox a close second in test paid for by Microsoft
By Ellen Messmer , Network World , 08/13/2009
Microsoft's Internet Explorer 8 rated tops among five browsers tested by NSS Labs for effectiveness in protecting against malware and phishing attacks—though NSS Labs acknowledges Microsoft paid for the tests.
Nevertheless, the test process, which lasted over a two-week period in July at the NSS Labs in Austin, evaluated the browsers based on access to live Internet sites and in theory could be duplicated elsewhere. Apple Safari 4, Google Chrome 2, Mozilla Firefox 3, and Opera 10 beta were evaluated as being behind Microsoft IE 8 when it comes to browser protection against phishing and malware, mainly because Microsoft was deemed more speedy and comprehensive in delivering updates about known phishing and malware to the user's desktop browser.
Slideshow: 15 Secrets of Next-Gen Browsers
Time is of the essence to use the browser as protective cover, one of the two NSS Labs reports issued Thursday notes. The report cites an Anti-Phishing Working Group estimate that more than 47,000 unique attacks occurred in the second half of 2008 with an average lifespan of 52 hours.
The test was based on 593 validated URLs. "The average phishing URL catch rate for browsers over the entire 14-day test period ranged from 2% for Safari 4 to 83% for Windows Internet Explorer 8," the test report states. "Internet Explorer 8 and Firefox 3 were the most consistent in the high level of protection they offered."
Firefox 3, which boasted 80% effectiveness in the phishing test, finished just behind IE 8's 83%. Coming in at third was the Opera 10 beta at 54%, followed by Chrome 2 at 26% and Safari 4 at 2 % in terms of mean block rate for phishing.
"Google Chrome's overall catch rate of 26% was below average," the "Web Browser Security: Phishing Comparison Comparative Results" report concludes. "We expected better results given the fanfare about Google's SafeBrowsing initiative . Additionally, a third-party (Firefox) was able to utilize Google API to achieve significantly better protection than Google's own browser."
In the testing for how well each of the five browsers provide protection against socially-engineered malware—defined as a Web page link that leads directly to a ‘download' that delivers a malicious payload whose content type would lead to execution—Microsoft was also found to perform the best.
In a test based on 608 potentially malicious URLs, IE 8 achieved an 81% mean block rate for socially-engineered malware, while Firefox 3 logged in at 27%, Safari 4 at 21%, Chrome 2 at 7% and Opera 10 beta at 1%. On average, 197 new validated URLs were added to the test each day, more or less depending on "criminal activity levels" as malicious URLs quickly rolled in and out of use.
IE Explorer 8, which calls its protection mechanism SmartScreen , did best for protecting against socially-engineered malware in what was called the "zero hour" timeframe when a malicious URL was spotted by blocking 51% of the time. By the fifth day of the known malicious URL, IE 8 was blocking 91% of the time, Firefox 3 24%, Safari 4 22% , Chrome 2 14% and Opera 10 beta 1%.
The report titled "Web browser Security: Socially Engineered Malware Protection Comparative Results 2nd Edition," points out that browser protection relies on two main functional components:
"an in-the-cloud reputation-based system which scours the Internet for malicious websites and categorizes content according" by adding it to a black or white list, or assigning a ‘score,' depending on the vendor's approach, which might be automated or manual or a combination of both.
"The second functional component resides with the Web browser and requests reputation information from in-the-cloud systems about specific URLs and then enforces warning and blocking functions."
Rick Moy, president of NSS Labs, says IE is continuing to improve its protection against cybercriminals based on a comparison with previous tests. The four other browsers in the tests generally "underperformed," he notes, with the exception of the Firefox browser phishing scores.
Moy says the Web browser is often viewed in terms of its potential vulnerabilities but it should also be looked at as "a potential layer of security."
All contents copyright 1995-2009 Network World, Inc. http://www.networkworld.com
55
Teknologi Informasi / Bug exposes eight years of Linux kernel
« on: 15 August 2009, 09:46:45 AM »
Source : http://www.theregister.co.uk/2009/08/14/critical_linux_bug/
Bug exposes eight years of Linux kernel
Track this topic Print story Post commentPasses it's-not-crying-wolf test
By Dan Goodin in San Francisco • Get more from this author
Posted in Security, 14th August 2009 00:54 GMT
Linux developers have issued a critical update for the open-source OS after researchers uncovered a vulnerability in its kernel that puts most versions built in the past eight years at risk of complete takeover.
The bug involves the way kernel-level routines such as sock_sendpage react when they are left unimplemented. Instead of linking to a corresponding placeholder, (for example, sock_no_accept), the function pointer is left uninitialized. Sock_sendpage doesn't always validate the pointer before dereferencing it, leaving the OS open to local privilege escalation that can completely compromise the underlying machine.
"Since it leads to the kernel executing code at NULL, the vulnerability is as trivial as it can get to exploit," security researcher Julien Tinnes writes here. "An attacker can just put code in the first page that will get executed with kernel privileges."
Tinnes and fellow researcher Tavis Ormandy released proof-of-concept code that they said took just a few minutes to adapt from a previous exploit they had. They said all 2.4 and 2.6 versions since May 2001 are affected.
Security researchers not involved in the discovery were still studying the advisory at time of writing, but at least one of them said it appeared at first blush to warrant immediate action.
"This passes my it's-not-crying-wolf test so far," said Rodney Thayer, CTO of security research firm Secorix. "If I had some kind of enterprise-class Linux system like a Red Hat Enterprise Linux...I would really go check and see if this looked like it related, and if my vendor was on top of it and did I need to get a kernel patch."
This is the second time in less than a month that a serious security vulnerability has been reported in the Linux kernel. In mid July, a researcher alerted Linux developers to a separate "NULL pointer dereference" bug that put newer versions at risk of complete compromise. The bug, which was located in several parts of the kernel, attracted plenty of notice because it bit even when SELinux, or Security-Enhanced Linux, implementations were running.
More about the latest vulnerability is here, and additional details about the patch are here.
Bug exposes eight years of Linux kernel
Track this topic Print story Post commentPasses it's-not-crying-wolf test
By Dan Goodin in San Francisco • Get more from this author
Posted in Security, 14th August 2009 00:54 GMT
Linux developers have issued a critical update for the open-source OS after researchers uncovered a vulnerability in its kernel that puts most versions built in the past eight years at risk of complete takeover.
The bug involves the way kernel-level routines such as sock_sendpage react when they are left unimplemented. Instead of linking to a corresponding placeholder, (for example, sock_no_accept), the function pointer is left uninitialized. Sock_sendpage doesn't always validate the pointer before dereferencing it, leaving the OS open to local privilege escalation that can completely compromise the underlying machine.
"Since it leads to the kernel executing code at NULL, the vulnerability is as trivial as it can get to exploit," security researcher Julien Tinnes writes here. "An attacker can just put code in the first page that will get executed with kernel privileges."
Tinnes and fellow researcher Tavis Ormandy released proof-of-concept code that they said took just a few minutes to adapt from a previous exploit they had. They said all 2.4 and 2.6 versions since May 2001 are affected.
Security researchers not involved in the discovery were still studying the advisory at time of writing, but at least one of them said it appeared at first blush to warrant immediate action.
"This passes my it's-not-crying-wolf test so far," said Rodney Thayer, CTO of security research firm Secorix. "If I had some kind of enterprise-class Linux system like a Red Hat Enterprise Linux...I would really go check and see if this looked like it related, and if my vendor was on top of it and did I need to get a kernel patch."
This is the second time in less than a month that a serious security vulnerability has been reported in the Linux kernel. In mid July, a researcher alerted Linux developers to a separate "NULL pointer dereference" bug that put newer versions at risk of complete compromise. The bug, which was located in several parts of the kernel, attracted plenty of notice because it bit even when SELinux, or Security-Enhanced Linux, implementations were running.
More about the latest vulnerability is here, and additional details about the patch are here.
56
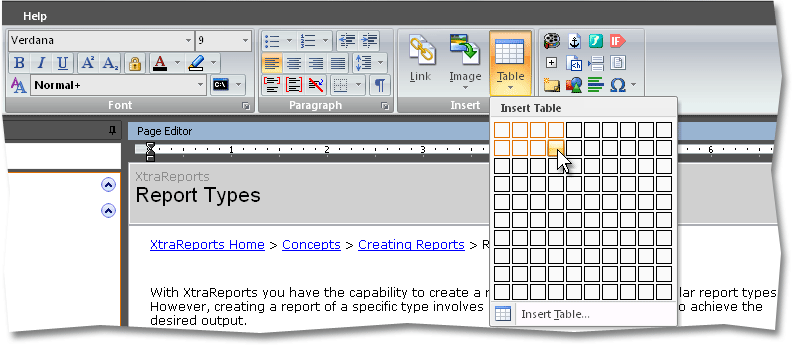
Teknologi Informasi / Delphi ain't dead yet
« on: 14 August 2009, 06:28:34 PM »
source : http://community.devexpress.com/blogs/dxram/archive/2009/07/31/delphi-ain-t-dead-yet.aspx?Newsletter8
I've heard people talking about the imminent death of Delphi for 15 years, and the language is only 14.5 years old. It seems that every year or so some wise guy lobs a bomb into the blogosphere like Rest In Peace Delphi.
But the reality is that commercial developers are using Delphi every day to build applications that we all probably use every day, and most users probably don't even know were written in Delphi.
It is true that over the past 8 years C# has been embraced by a lot of corporate development shops (some ex-Delphi, probably many more ex-Java), because in an homogenous environment where you can control that every deployment will be to Vista with .NET 3.5 pre-installed and a common path to a local SQL server, a C# (or VB.NET) application is the path of least resistance. But there are environments where a native Delphi application maintains a distinct advantage.
Shrink Wrapped applications
One strength of Delphi is that you compile into a windows executable, and your app just runs on almost every version of Windows built in the past decade. No need for a specific version of an application deployment framework (like .NET) to be available.
Nick Bradbury, who you may know as the developer of commercial hits like HomeSite and TopStyle uses Delphi and gives probably the best rationale on his blog for a micro-ISV developing applications choosing Delphi.
You may have also noticed the recent testimonial from EC Software the developers of Help&Manual who use ExpressBars to build a new revolutionary UI in their Delphi application.
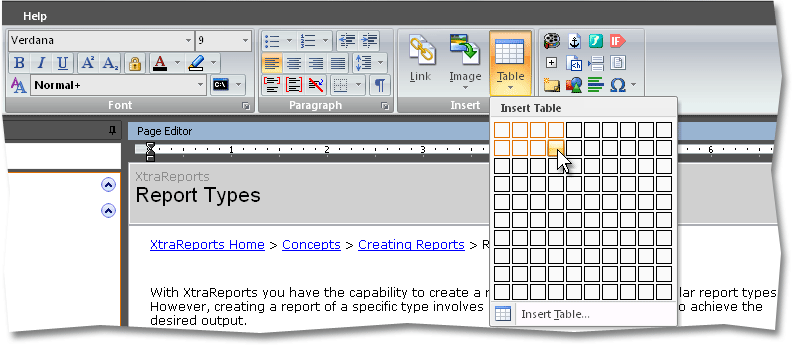
Delphi is a good choice for creating shrink wrapped applications, or shareware applications for Windows, or just generally any application for deployment to a heterogeneous windows environment.
Real-time applications
Delphi allows the same kind of "to the metal" control of hardware as any Microsoft C++ application that would be impossible in a platform abstracted away from the hardware like Java or C#.
You may know Developer Express is a geographically diverse company, with developers and evangelists spread around the globe (even the outback of Australia). We use email, and IMs to communicate and coordinate but when text is just not rich enough we use Skype which was built in Delphi.
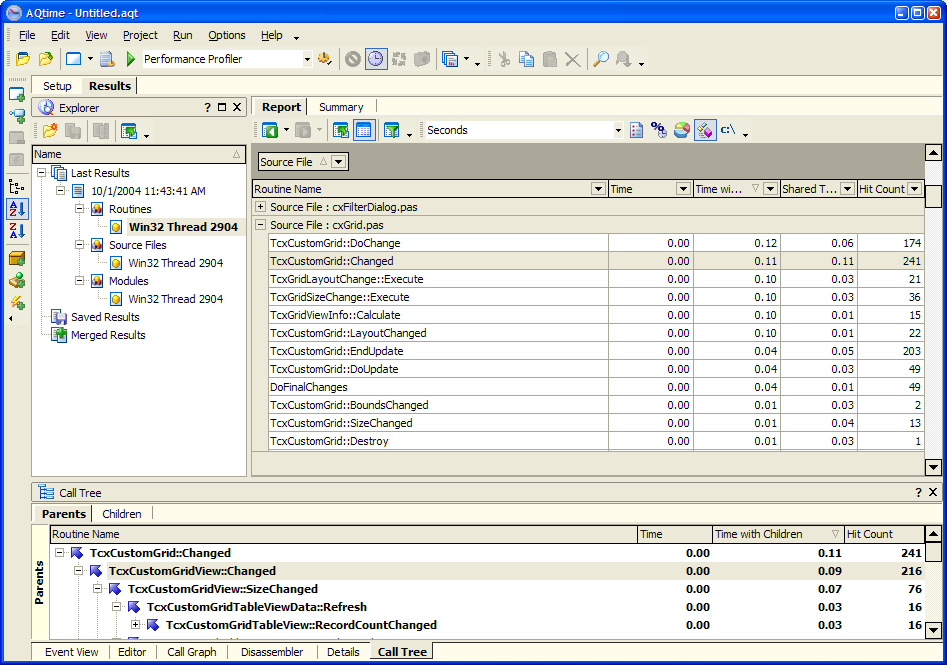
Test Complete from AutomatedQA was built entirely in Delphi and is able to produce millisecond resolution automated testing for any kind of application development.
If you are building applications like these that have to be responsible for the number of CPU cycles they consume, Delphi may be a good choice.
Component based development
Sure you could build real time apps like Skype, or Shrink Wrapped apps like HomeSite in MicroSoft C++ but if your competitor is using Delphi they will leave you in the dust because they can leverage a broad palette of drop in components from third party companies like Developer Express that will propel an application development closer to completion.
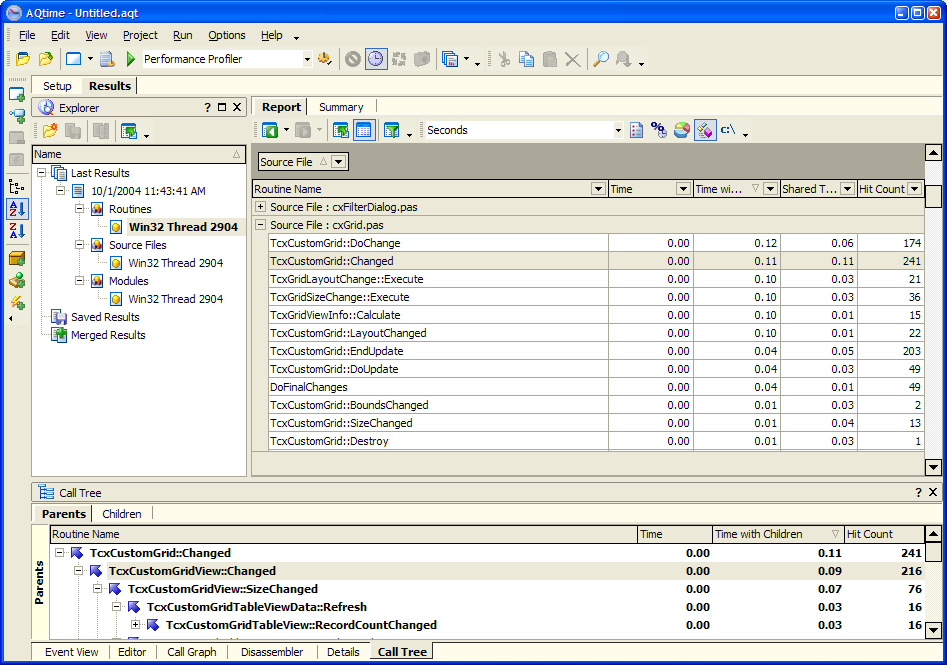
Imagine if you were trying to compete with Quests all purpose Database tool TOAD using something other than Delphi and didn't have the luxury of being able to drop in a component like the Express QuantumGrid with all it's sorting/grouping/filtering and master/detail functionality at your fingertips.
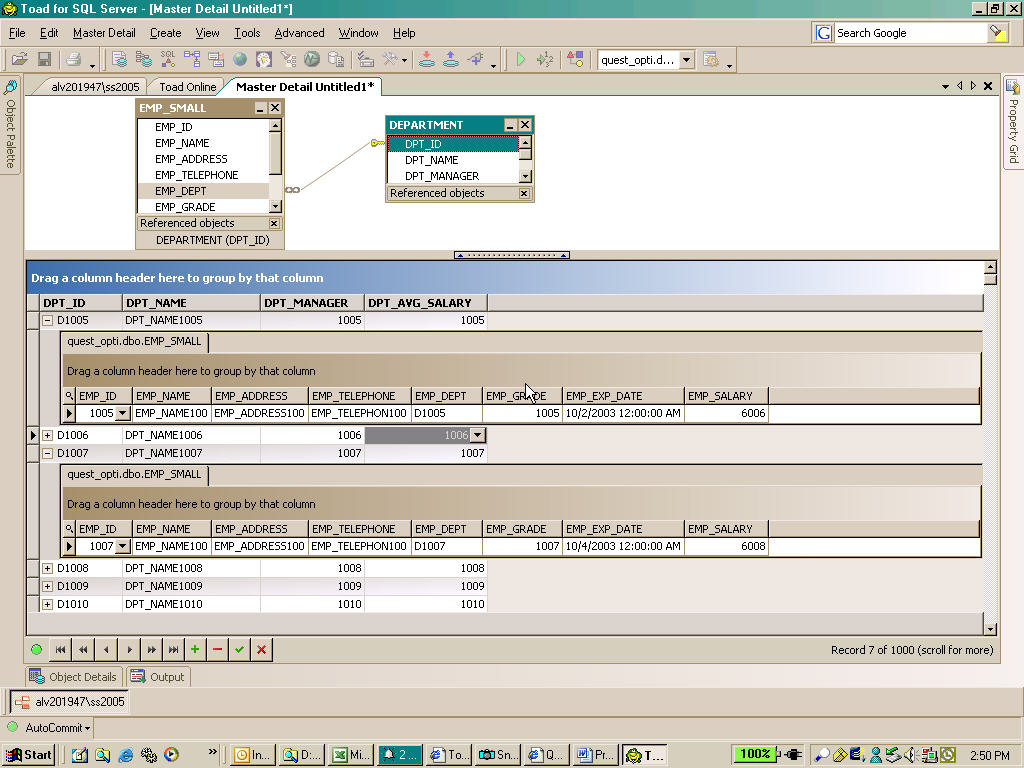
It would take a team of developers several years just to build that functionality (http://www.devexpress.com/Products/VCL/ExQuantumGrid/) - and yet any Delphi developer can buy a component for $399 and drop it into his application and be there already.
Delphi Community
Finally there is an entire ecosystem of commercial developers making a good living from supporting Delphi, from CodeGear who are always working to extend the language, to companies like Developer Express building broad offerings of components, and even companies like Quest and Automated QA building developer tools using Delphi. Here at DevExpress we have a commited team of developers that just love working with, and extending Delphi ... it's not as big a market as .NET is for us, but many of us were also Delphi developers before .NET and still use Delphi regularly.
Sure there are some scenarios where .NET has significant advantages over Delphi (Prism, which is both, is a subject for another blog post) - heck there are many scenarios where Ruby on Rails is a better platform than Delphi - but there are definite problems for which Delphi is a good solution.
Like Mark Twain, it seems that the rumors of the death of Delphi have been greatly exaggerated.
Published Jul 31 2009, 09:00 AM by Richard Morris (Developer Express) Filed under: delphi
Technorati tags: delphi
I've heard people talking about the imminent death of Delphi for 15 years, and the language is only 14.5 years old. It seems that every year or so some wise guy lobs a bomb into the blogosphere like Rest In Peace Delphi.
But the reality is that commercial developers are using Delphi every day to build applications that we all probably use every day, and most users probably don't even know were written in Delphi.
It is true that over the past 8 years C# has been embraced by a lot of corporate development shops (some ex-Delphi, probably many more ex-Java), because in an homogenous environment where you can control that every deployment will be to Vista with .NET 3.5 pre-installed and a common path to a local SQL server, a C# (or VB.NET) application is the path of least resistance. But there are environments where a native Delphi application maintains a distinct advantage.
Shrink Wrapped applications
One strength of Delphi is that you compile into a windows executable, and your app just runs on almost every version of Windows built in the past decade. No need for a specific version of an application deployment framework (like .NET) to be available.
Nick Bradbury, who you may know as the developer of commercial hits like HomeSite and TopStyle uses Delphi and gives probably the best rationale on his blog for a micro-ISV developing applications choosing Delphi.
You may have also noticed the recent testimonial from EC Software the developers of Help&Manual who use ExpressBars to build a new revolutionary UI in their Delphi application.
Delphi is a good choice for creating shrink wrapped applications, or shareware applications for Windows, or just generally any application for deployment to a heterogeneous windows environment.
Real-time applications
Delphi allows the same kind of "to the metal" control of hardware as any Microsoft C++ application that would be impossible in a platform abstracted away from the hardware like Java or C#.
You may know Developer Express is a geographically diverse company, with developers and evangelists spread around the globe (even the outback of Australia). We use email, and IMs to communicate and coordinate but when text is just not rich enough we use Skype which was built in Delphi.
Test Complete from AutomatedQA was built entirely in Delphi and is able to produce millisecond resolution automated testing for any kind of application development.
If you are building applications like these that have to be responsible for the number of CPU cycles they consume, Delphi may be a good choice.
Component based development
Sure you could build real time apps like Skype, or Shrink Wrapped apps like HomeSite in MicroSoft C++ but if your competitor is using Delphi they will leave you in the dust because they can leverage a broad palette of drop in components from third party companies like Developer Express that will propel an application development closer to completion.
Imagine if you were trying to compete with Quests all purpose Database tool TOAD using something other than Delphi and didn't have the luxury of being able to drop in a component like the Express QuantumGrid with all it's sorting/grouping/filtering and master/detail functionality at your fingertips.
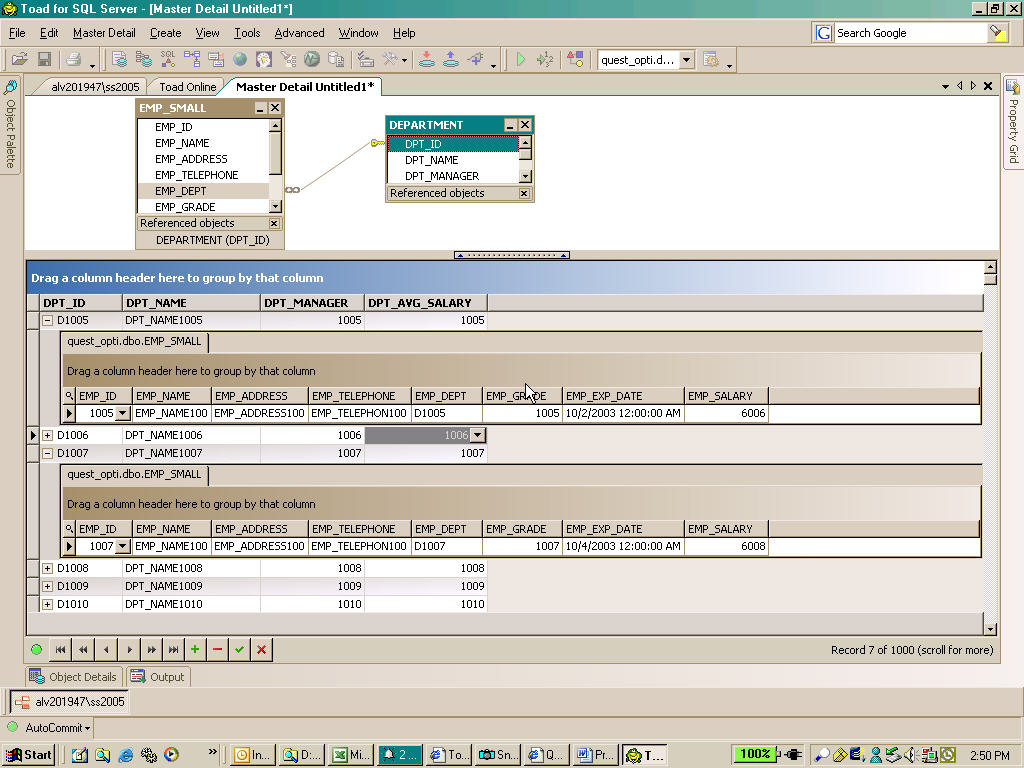
It would take a team of developers several years just to build that functionality (http://www.devexpress.com/Products/VCL/ExQuantumGrid/) - and yet any Delphi developer can buy a component for $399 and drop it into his application and be there already.
Delphi Community
Finally there is an entire ecosystem of commercial developers making a good living from supporting Delphi, from CodeGear who are always working to extend the language, to companies like Developer Express building broad offerings of components, and even companies like Quest and Automated QA building developer tools using Delphi. Here at DevExpress we have a commited team of developers that just love working with, and extending Delphi ... it's not as big a market as .NET is for us, but many of us were also Delphi developers before .NET and still use Delphi regularly.
Sure there are some scenarios where .NET has significant advantages over Delphi (Prism, which is both, is a subject for another blog post) - heck there are many scenarios where Ruby on Rails is a better platform than Delphi - but there are definite problems for which Delphi is a good solution.
Like Mark Twain, it seems that the rumors of the death of Delphi have been greatly exaggerated.
Published Jul 31 2009, 09:00 AM by Richard Morris (Developer Express) Filed under: delphi
Technorati tags: delphi
57
Teknologi Informasi / lifetimes of hard disk drives.
« on: 14 August 2009, 06:24:15 PM »
Back in 2007 Google released a study on the lifetimes of hard disk drives. They are obviously in a pretty unique position to do so since they run huge server farms that run the majority of the world's searches, emails, and other cloud-like services.
Although they didn't single out any particular manufacturer or brand as being better or worse than the norm, they did say that a new disk drive has about a 2% chance of failing in a year. Drives that are over 2 or 3 years old the rate is significantly higher, over 8%.
Let's take that lower probability, and run with it.
So, the disk in your newish laptop has a one in 50 chance of dying this year. Doesn't sound too bad, surely? That's like shuffling a pack of cards thoroughly, placing the pack on the table, cutting, turning over the top card and it being the ace of spades.
Taking it further: in our house we have several PCs, containing in all 8 newish disk drives spinning all the time. The probability that at least one of those 8 dying this year according to Google's probability is 15%.
One in 7. That's in between tossing three heads in a row with a coin or throwing a six on a single die. Suddenly it doesn't seem that remote any more. (If they were older, that becomes 1 chance in 2 that at least one drive would fail.)
So, when was the last time you backed up? Given that, like me, you're the free tech gopher for all your relatives' and friends' machines, when did they back up?
Julian M Bucknall, CTO
Although they didn't single out any particular manufacturer or brand as being better or worse than the norm, they did say that a new disk drive has about a 2% chance of failing in a year. Drives that are over 2 or 3 years old the rate is significantly higher, over 8%.
Let's take that lower probability, and run with it.
So, the disk in your newish laptop has a one in 50 chance of dying this year. Doesn't sound too bad, surely? That's like shuffling a pack of cards thoroughly, placing the pack on the table, cutting, turning over the top card and it being the ace of spades.
Taking it further: in our house we have several PCs, containing in all 8 newish disk drives spinning all the time. The probability that at least one of those 8 dying this year according to Google's probability is 15%.
One in 7. That's in between tossing three heads in a row with a coin or throwing a six on a single die. Suddenly it doesn't seem that remote any more. (If they were older, that becomes 1 chance in 2 that at least one drive would fail.)
So, when was the last time you backed up? Given that, like me, you're the free tech gopher for all your relatives' and friends' machines, when did they back up?
Julian M Bucknall, CTO
58
Diskusi Umum / Born To Be Free
« on: 13 August 2009, 10:00:50 AM »
Banyak kenyataan hidup yg tidak dapat kita terima (penolakan=dosa), membuat kita mempelajari arti hidup buat kita.
Kalau kita hanya terus berpikir terhadap kehidupan kita, maka arti hidup tidak akan kita temui, yg malah akan berujung pada penyesalan terhadap waktu yg sudah kita buang, yg tidak kita manfaatkan dengan baik karena kita masih terikat konsep Aku, sehingga selalu berpikir... "jika saja aku...."
hal tersebut sangat membebani pikiran, dan membuat kita sulit untuk berkonsentrasi untuk memikirkan masa depan, karena masa depan bagi si Aku adalah pasti. Yaitu Kematian.
Setiap hari berpikir tentang kematian, perubahan serta hal2 yg tidak akan kita lihat, dengar, cium, sapa, lagi, seseorang yg tidak akan kita beri senyum lagi, walau hanya untuk bertegur sapa. Hal2 tersebut membebani hidup, banyak dari rekan2 atau teman2 atau dari majalah atau dari ceramah2 orang.. kalau kita harus melepas beban kita,,,
namun mereka lupa memberikan kata kuncinya , passwordnya...
Melepas beban2 seperti itu tidaklah mudah, karena hal2 tersebut memang kenyataan yg ada.. bagaimana kita mungkin melepas kenyataan begitu saja..
maka itu kita butuh reasonable reason.. suatu alasan yg dapat kita terima, agar kita dapat melepas beban tersebut...
yaitu adalah dengan percaya akan konsep Anicca, Dukkha dan Anatta
Anicca, yaitu Melihat suatu kenyataan dan fenomena yg ada sebagaimana adanya,, yaitu tidak kekal dan selalu berubah....
Dukkha, yaitu Semua fenomena itu adalah ilusi yg berujung pada ketidakpuasan dan penderitaan
Anatta, yg melihat "Aku" sebagai hal yg tidak penting, begitu pula diri kita.... karena si "Aku" itu hanya hidup sekali saja...
dengan begitu kita tidak lagi mengharapkan lagi si "AKu" karena dia tidaklah penting.
Namun ada hal yg kurang, ada penghubung serta pelengkap yg kurang, yaitu tujuan...
beruntunglah kita guru Buddha sudah memberikan petunjuk2 akan tujuan kita....
seperti guru buddha, dia tidak terlahir sebagai seorang buddha hanya karena terpilih... tetapi memang karena kumpulan jasa2 baik beliau... dari kehidupan yg lalu nya.
saat beliau tidak mempunyai tekad untuk menjadi seorang buddha, beliau hanyalah makhluk biasa, yg selalu berbuat baik namun masih tanpa tujuan,
sampai beliau bertekad untuk menjadi Buddha, sehingga beliau dari satu kehidupan dan kehidupan lainnya selalu menambah kebaikan, dan kebijaksanaan sedikit demi sedikit.... sampai berpuluh2, beratus2, beribu2 kehidupan.... beliau tidak pernah lelah mengorbankan si "Aku" dalam kehidupannya...
Karena beliau percaya bahwa kelak paraminya akan cukup untuk mendukung beliau menjadi seorang buddha. Banyak sekali pengorbanan yg dilakukan oleh "si Aku" Buddha Gotama pada kehidupan lalunya... mereka mengorbankan waktunya, dagingnya, serta kehidupannya...
Sungguh suatu cerita yg sangat menggugah hati....
Lalu bagaimana dengan kita?
Apakah kita masih memikirkan "Kualitas hidup AKU-ku apakah baik?"
Marilah rekan2, kita korbankan ke-AKU-an kita, karena si "AKU" hidup hanya untuk mati, namun jatidiri kita hidup untuk bebas...
"BORN TO BE FREE"
Kita hidup untuk mencari kebebasan nibbana, dan hidup sebagai manusia hanyalah sekian permainan dalam beribu2 permainan yg akan kita jalani,
janganlah lelah, dan jangan sia siakan hidup yg kita punya sekarang ini hanya untuk si Aku yg berumur singkat, namun hiduplah demi kebebasan yg akan kita tuju, yg akan kita raih, kumpulkanlah Parami kita, karena dengan begitu kita akan bermain lebih baik lagi di kehidupan berikutnya, berikutnya, berikutnya.... sampai kita terbebas....
Kalau kita hanya terus berpikir terhadap kehidupan kita, maka arti hidup tidak akan kita temui, yg malah akan berujung pada penyesalan terhadap waktu yg sudah kita buang, yg tidak kita manfaatkan dengan baik karena kita masih terikat konsep Aku, sehingga selalu berpikir... "jika saja aku...."
hal tersebut sangat membebani pikiran, dan membuat kita sulit untuk berkonsentrasi untuk memikirkan masa depan, karena masa depan bagi si Aku adalah pasti. Yaitu Kematian.
Setiap hari berpikir tentang kematian, perubahan serta hal2 yg tidak akan kita lihat, dengar, cium, sapa, lagi, seseorang yg tidak akan kita beri senyum lagi, walau hanya untuk bertegur sapa. Hal2 tersebut membebani hidup, banyak dari rekan2 atau teman2 atau dari majalah atau dari ceramah2 orang.. kalau kita harus melepas beban kita,,,
namun mereka lupa memberikan kata kuncinya , passwordnya...
Melepas beban2 seperti itu tidaklah mudah, karena hal2 tersebut memang kenyataan yg ada.. bagaimana kita mungkin melepas kenyataan begitu saja..
maka itu kita butuh reasonable reason.. suatu alasan yg dapat kita terima, agar kita dapat melepas beban tersebut...
yaitu adalah dengan percaya akan konsep Anicca, Dukkha dan Anatta
Anicca, yaitu Melihat suatu kenyataan dan fenomena yg ada sebagaimana adanya,, yaitu tidak kekal dan selalu berubah....
Dukkha, yaitu Semua fenomena itu adalah ilusi yg berujung pada ketidakpuasan dan penderitaan
Anatta, yg melihat "Aku" sebagai hal yg tidak penting, begitu pula diri kita.... karena si "Aku" itu hanya hidup sekali saja...
dengan begitu kita tidak lagi mengharapkan lagi si "AKu" karena dia tidaklah penting.
Namun ada hal yg kurang, ada penghubung serta pelengkap yg kurang, yaitu tujuan...
beruntunglah kita guru Buddha sudah memberikan petunjuk2 akan tujuan kita....
seperti guru buddha, dia tidak terlahir sebagai seorang buddha hanya karena terpilih... tetapi memang karena kumpulan jasa2 baik beliau... dari kehidupan yg lalu nya.
saat beliau tidak mempunyai tekad untuk menjadi seorang buddha, beliau hanyalah makhluk biasa, yg selalu berbuat baik namun masih tanpa tujuan,
sampai beliau bertekad untuk menjadi Buddha, sehingga beliau dari satu kehidupan dan kehidupan lainnya selalu menambah kebaikan, dan kebijaksanaan sedikit demi sedikit.... sampai berpuluh2, beratus2, beribu2 kehidupan.... beliau tidak pernah lelah mengorbankan si "Aku" dalam kehidupannya...
Karena beliau percaya bahwa kelak paraminya akan cukup untuk mendukung beliau menjadi seorang buddha. Banyak sekali pengorbanan yg dilakukan oleh "si Aku" Buddha Gotama pada kehidupan lalunya... mereka mengorbankan waktunya, dagingnya, serta kehidupannya...
Sungguh suatu cerita yg sangat menggugah hati....
Lalu bagaimana dengan kita?
Apakah kita masih memikirkan "Kualitas hidup AKU-ku apakah baik?"
Marilah rekan2, kita korbankan ke-AKU-an kita, karena si "AKU" hidup hanya untuk mati, namun jatidiri kita hidup untuk bebas...
"BORN TO BE FREE"
Kita hidup untuk mencari kebebasan nibbana, dan hidup sebagai manusia hanyalah sekian permainan dalam beribu2 permainan yg akan kita jalani,
janganlah lelah, dan jangan sia siakan hidup yg kita punya sekarang ini hanya untuk si Aku yg berumur singkat, namun hiduplah demi kebebasan yg akan kita tuju, yg akan kita raih, kumpulkanlah Parami kita, karena dengan begitu kita akan bermain lebih baik lagi di kehidupan berikutnya, berikutnya, berikutnya.... sampai kita terbebas....
59
Buddhisme dengan Agama, Kepercayaan, Tradisi dan Filsafat Lain / "God exists" is a scientific claim
« on: 07 August 2009, 10:45:16 AM »
copas dari eFBe 

Quote
From The God Delusion:
http://www.edge.org/3rd_culture/dawkins06/dawkins06_index.html
-------
[Theists] are apt to quote the late Stephen Jay Gould's 'NOMA' — 'non-overlapping magisteria'. Gould claimed that science and true religion never come into conflict because they exist in completely separate dimensions of discourse:
"To say it for all my colleagues and for the umpteenth millionth time (from college bull sessions to learned treatises): science simply cannot (by its legitimate methods) adjudicate the issue of God's possible superintendence of nature. We neither affirm nor deny it; we simply can't comment on it as scientists."
This sounds terrific, right up until you give it a moment's thought. You then realize that the presence of a creative deity in the universe is clearly a scientific hypothesis. Indeed, it is hard to imagine a more momentous hypothesis in all of science. A universe with a god would be a completely different kind of universe from one without, and it would be a scientific difference. God could clinch the matter in his favour at any moment by staging a spectacular demonstration of his powers, one that would satisfy the exacting standards of science. Even the infamous Templeton Foundation recognized that God is a scientific hypothesis — by funding double-blind trials to test whether remote prayer would speed the recovery of heart patients. It didn't, of course, although a control group who knew they had been prayed for tended to get worse (how about a class action suit against the Templeton Foundation?) Despite such well-financed efforts, no evidence for God's existence has yet appeared.
To see the disingenuous hypocrisy of religious people who embrace NOMA, imagine that forensic archeologists, by some unlikely set of circumstances, discovered DNA evidence demonstrating that was born of a virgin mother and had no father. If NOMA enthusiasts were sincere, they should dismiss the archeologists' DNA out of hand: "Irrelevant. Scientific evidence has no bearing on theological questions. Wrong magisterium." Does anyone seriously imagine that they would say anything remotely like that? You can bet your boots that not just the fundamentalists but every professor of theology and every bishop in the land would trumpet the archeological evidence to the skies.
Either had a father or he didn't. The question is a scientific one, and scientific evidence, if any were available, would be used to settle it. The same is true of any miracle — and the deliberate and intentional creation of the universe would have to have been the mother and father of all miracles. Either it happened or it didn't. It is a fact, one way or the other, and in our state of uncertainty we can put a probability on it — an estimate that may change as more information comes in.
-------
Since the god hypothesis is a scientific claim, we can compare it to other scientific claims. It's completely inappropriate to grant god the free pass that theists have bestowed upon him for millenia.
With what's implied in the claim "god exists" and what we know to be true about the universe, the only way the probability of god existing can be greater than ZERO is to abandon intellectual honesty and give god a free pass.
Discuss.
60
Bantuan Teknis, kritik dan saran. / tanya klasifikasi thread
« on: 06 August 2009, 02:04:03 PM »
di setiap board kan ada keterangannya tuh..
nah contoh di buddhisme untuk pemula disitu keterangannya buat pertanyaan2 pemula...
namun di Starter thread nya ada yg berupa artikel2...
contoh
http://dhammacitta.org/forum/index.php/topic,12339.0.html
http://dhammacitta.org/forum/index.php/topic,12266.0.html
http://dhammacitta.org/forum/index.php/topic,12332.0.html
http://dhammacitta.org/forum/index.php/topic,12268.0.html
nah ini gmana neh benernya.. apa salah tempat atau keterangannya yg rancu?
nah contoh di buddhisme untuk pemula disitu keterangannya buat pertanyaan2 pemula...
namun di Starter thread nya ada yg berupa artikel2...
contoh
http://dhammacitta.org/forum/index.php/topic,12339.0.html
http://dhammacitta.org/forum/index.php/topic,12266.0.html
http://dhammacitta.org/forum/index.php/topic,12332.0.html
http://dhammacitta.org/forum/index.php/topic,12268.0.html
nah ini gmana neh benernya.. apa salah tempat atau keterangannya yg rancu?